Part 3B - Creating the Microsoft CA Template for Subordinate CA certificates in vSphere 6.0
Active Directory Certificate Authority Certificates Microsoft
Published on 24 March 2016 by Christopher Lewis. Words: 317. Reading Time: 2 mins.
This is Part 3B of a series of posts on how to configure VMware vSphere 6.x to use Certificates from Microsoft Windows Server Certificate Services, covering the creation of a Subordinate CA certificate for use with the VMware Certificate Authority (VMCA).
For some insightful information on VMCA Design Decisions post by AtherBeg
The following assumes you have completed the steps within the series:
- Part 1 - Installing Microsoft Windows 2012 R2 Certificate Services
- Part 2 - Configuring an Enterprise Root Certificate Authority
- Part 3A - Creating the Microsoft CA Template for SSL certificates in vSphere 6.0
The high level steps below are taken from the VMware KB Article Creating a Microsoft Certificate Authority Template for SSL certificate creation in vSphere 6.0 .
Instructions
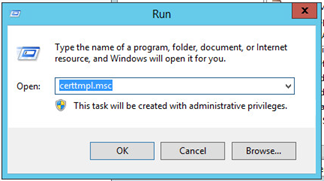
Open the Certificate Template Console by running certtmpl.msc
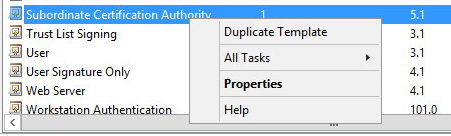
From within the Certificate Template Console, locate the Subordinate Certification Authority template, right click and select Duplicate Template.
At the Properties of New Template window, select the Compatibility Tab and set the appropriate Compatibility Settings or leave as default.

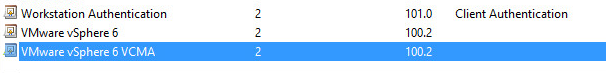
At the Properties of New Template window, select the **General **Tab and set the Template Display Name to VMware vSphere 6 VCMA, (if appropriate) update Validity period (default is 5 years) and check the Publish certificate in Active Directory checkbox.

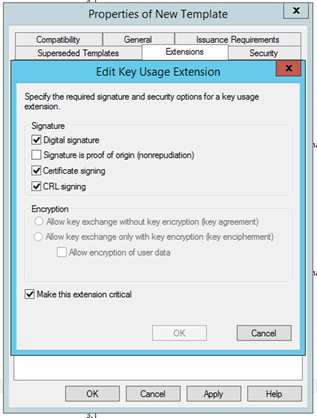
At the Properties of New Template window, select the Extensions Tab and select Key Usage and click Edit.

At the Edit Key Usage Extension dialog, ensure that the Digital signature, Certificate signing and CRL signing checkboxes are checked and then check the Make this extension critical checkbox and click OK.
At the Properties of New Template dialog, click OK to save the new Certificate Template.

The new VMware vSphere 6 VCMA template should now be visible within the Certificate Template Console.
Next Steps
In Part 4 , I will cover how to enable the new Certificate Templates so that you can finally go and create SSL certificates!
Published on 24 March 2016 by Christopher Lewis. Words: 317. Reading Time: 2 mins.